HELOO TWIN TULIPS FAMILY ON BINANCE SQUARE Dusk Coin: Token Economics and Incentive Alignment in Privacy Blockchains
Privacy has quietly returned to the center of the blockchain conversation. As institutions explore on-chain finance and regulators demand compliance-ready infrastructure, privacy-focused blockchains are being forced to evolve. Dusk Network is one of the projects attempting to bridge that gap, positioning itself as a privacy-preserving blockchain built for real-world financial use cases.
At the heart of this design is DUSK, the network’s native token. Understanding how DUSK is structured, distributed, and used is essential to evaluating whether the network’s incentives are aligned for long-term sustainability.
This article takes a closer look at Dusk Coin’s token economics and how it supports incentive alignment across users, validators, and developers in a privacy-first blockchain environment.
The Role of DUSK in the Network
DUSK is not a passive utility token. It plays an active role in nearly every layer of the Dusk Network.
At a high level, DUSK is used for:
Securing the network through staking
Paying transaction and execution fees
Incentivizing validators and participants
Enabling governance and long-term alignment
Because Dusk is built around confidential smart contracts and private asset issuance, its token must support both economic security and usability without undermining privacy guarantees.
Supply Structure and Emission Model
Dusk Network uses a capped token supply model, designed to balance scarcity with predictable issuance. Rather than aggressive inflation, DUSK emissions are primarily directed toward network security and validator participation.
New tokens enter circulation mainly through:
Staking rewards
Validator incentives
Network participation rewards
This approach ensures that inflation is tied directly to productive activity. Tokens are not printed arbitrarily; they are issued to actors who actively contribute to network security and reliability.
Over time, as the network matures and transaction fees increase, the reliance on new token issuance is expected to decrease. This transition mirrors the broader trend in blockchain economics: moving from inflation-driven security to fee-driven sustainability.
Staking and Validator Incentives
Dusk Network operates on a proof-of-stake consensus mechanism tailored for privacy-preserving computation. Validators must stake DUSK to participate in block production and consensus.
The incentive design here is straightforward but effective:
Validators earn rewards for honest participation
Misbehavior risks stake penalties or removal
Higher stake improves reliability but does not centralize control
By requiring skin in the game, the network discourages malicious behavior while rewarding long-term commitment. Validators are incentivized not just to remain online, but to process transactions accurately and maintain network uptime.
For delegators, staking offers a way to participate in network security without running infrastructure, aligning retail token holders with the health of the ecosystem.
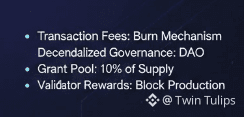
Transaction Fees and Economic Flow
Transaction fees on Dusk serve multiple purposes. They compensate validators, prevent spam, and establish real economic demand for the token.
Because Dusk focuses on confidential transactions and private smart contracts, execution costs reflect the complexity of zero-knowledge computations. Fees are designed to be predictable, avoiding sudden spikes that could price out legitimate users.
A portion of transaction fees flows directly to validators, while another portion supports long-term protocol sustainability. This creates a closed economic loop where usage directly strengthens network security.
As more assets, financial instruments, and applications are deployed on Dusk, transactional demand for DUSK increases organically rather than through artificial incentives.
Incentive Alignment for Privacy Applications
One of the most overlooked aspects of privacy blockchains is developer incentives. Dusk’s token model is structured to encourage the creation of compliant, privacy-preserving financial applications rather than purely experimental tooling.
Developers benefit from:
A predictable fee environment
Access to privacy-native smart contracts
An audience focused on real-world financial use cases
Because applications often require DUSK for execution and interaction, builders are incentivized to design efficient contracts that reduce unnecessary computational costs. This aligns developer behavior with user experience and network scalability.
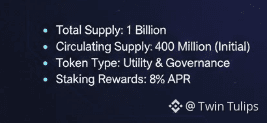
Governance and Long-Term Alignment
DUSK also plays a role in governance, allowing stakeholders to influence protocol upgrades, parameter changes, and network direction. While governance mechanisms evolve over time, the core principle remains consistent: those with long-term exposure to the network should help shape its future.
This discourages short-term speculation-driven decision-making and instead promotes policies that support sustainable growth, regulatory compatibility, and technical resilience.
Comparing Dusk’s Model to Other Privacy Chains
Unlike older privacy coins that rely primarily on transactional anonymity, Dusk positions privacy as infrastructure for financial markets. This distinction is reflected in its token economics.
Where some privacy networks emphasize transaction volume at all costs, Dusk prioritizes:
Validator reliability over raw throughput
Compliance-aware privacy over absolute opacity
Economic alignment over aggressive emissions
This results in a more conservative, institution-friendly incentive structure, which may sacrifice short-term hype in exchange for long-term relevance.
Final Thoughts
Token economics are ultimately a reflection of a project’s values. In Dusk Network’s case, the DUSK token is designed to support privacy without sacrificing accountability, security, or sustainability.
By tying issuance to participation, rewarding honest validators, and anchoring demand in real network usage, Dusk attempts to solve one of the hardest problems in blockchain design: aligning incentives in a system where privacy is a feature, not a loophole.
Whether this model succeeds will depend on adoption, developer activity, and real-world use cases. But from a structural standpoint, D
