When people talk about “governance tokens,” the discussion often stays abstract. Voting. Parameters. Decentralization. In practice, what matters is far more concrete: what exactly can be changed, who can change it, and what stops a bad actor from pushing something destructive through.
With WAL, these questions are not theoretical. WAL is used across payment flows, staking, and governance for Walrus Sites and the underlying network. That makes governance powerful by design, but also sensitive. In this article, I want to slow down and examine, in practical terms, what “key parameters and penalty settings” actually mean in the WAL governance context, and whether an attacker could realistically pass a proposal like setting slashing to 100% for all participants.
I’m writing this reflectively, not to defend or promote WAL, but to understand where governance power ends and where protocol safety mechanisms begin.
How WAL Governance Is Intended to Function
At its core, WAL governance exists to let stakeholders adjust economic and operational parameters without redeploying the protocol or relying on a centralized operator. That sounds straightforward, but it hides an important distinction: governance is about tuning, not rewriting, the system.
In practice, WAL token voting is designed to apply to parameters that are:
Quantitative rather than structural
Bounded rather than arbitrary
Constrained by protocol-level validation
This distinction matters because it defines what governance cannot do just as much as what it can.
When I look at WAL governance through this lens, I see a system that treats voting as a control surface, not a root-access console.
Categories of Parameters Subject to WAL Token Voting
Although exact parameter names may evolve, governance-controlled settings generally fall into a few well-understood categories.
Economic Parameters
These are the most visible and often the most debated. They include:
Base fees for storage, access, or publishing on Walrus Sites
Reward distribution ratios between node operators and other roles
Staking reward curves or emission modifiers within predefined ranges
What’s important here is that these parameters usually sit within hard-coded bounds. Governance can move values within a range, but it cannot redefine the range itself.
For example, a staking reward multiplier might be adjustable between 0.8× and 1.2×. Governance can choose where in that band the network operates, but it cannot vote rewards to zero or infinity unless the protocol explicitly allows it.
Penalty and Slashing Parameters
This is where concerns tend to concentrate, especially when people imagine worst-case governance attacks.
Penalty-related parameters may include:
Slashing percentages for provable misbehavior
Time-based penalties for downtime or missed attestations
Thresholds that trigger warnings versus actual slashing
However, slashing parameters are almost never unbounded. From a protocol safety perspective, they are typically constrained by:
Maximum slashing caps
Misbehavior-specific conditions
Multi-step enforcement logic
In other words, WAL governance may influence how severe penalties are, but not whether arbitrary slashing can occur.
Operational Thresholds and Limits
Another class of parameters affects how the network operates day to day:
Minimum stake required to participate as a node
Quorum thresholds for governance proposals
Voting periods and execution delays
These parameters shape governance itself. Changing them has second-order effects, which is why they are often more tightly controlled than economic knobs.
What Governance Cannot Directly Change
To understand whether a malicious proposal could succeed, it helps to be explicit about what governance does not touch.
Governance generally does not have the authority to:
Modify core validation logic
Change how misbehavior is detected
Bypass cryptographic checks
Execute arbitrary code on nodes
These elements live at the protocol level and require coordinated software upgrades, not token votes.
This separation is deliberate. If token voting alone could redefine slashing logic or force arbitrary state changes, the system would be fragile by design.
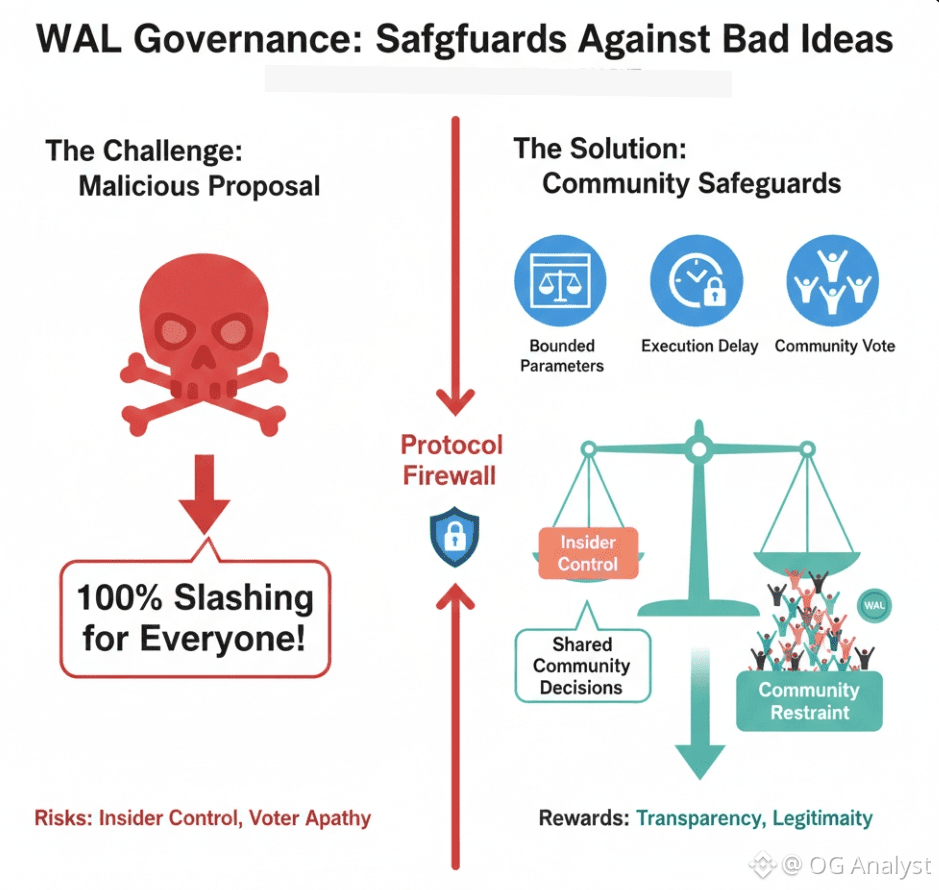
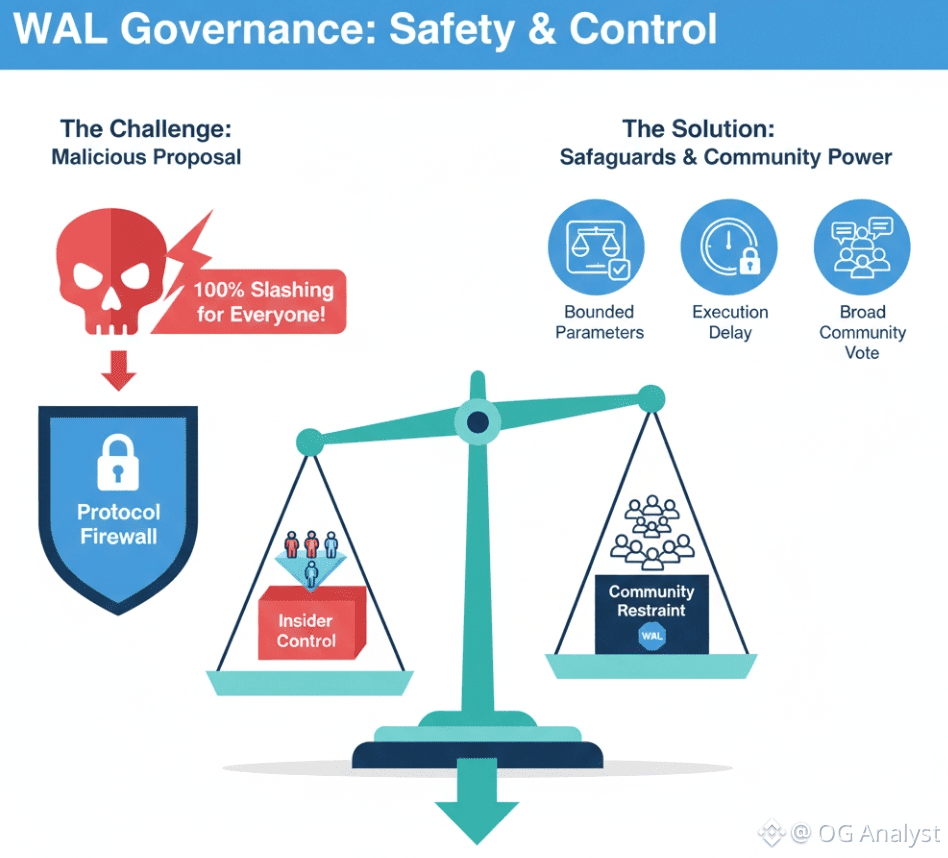
The Hypothetical Attack: “Set Slashing to 100% for All”
Let’s examine the scenario directly.
Could an attacker submit a proposal that sets slashing penalties to 100% for all participants and push it through governance?
On the surface, this sounds terrifying. In practice, several layers make this outcome extremely unlikely.
1. Parameter Bounding at the Protocol Level
The first and most important constraint is that governance proposals are validated against protocol-defined bounds.
If the maximum allowable slashing rate is, for example, 10% per offense, a proposal attempting to set it to 100% would be invalid at execution time, regardless of how many votes it receives.
This is a critical point that often gets missed. Voting power does not override code constraints.
2. Conditional Slashing, Not Global Slashing
Slashing is typically tied to specific, provable actions, such as:
Signing conflicting states
Submitting invalid proofs
Persistent downtime beyond thresholds
Even if governance increased slashing severity to the upper bound, it would still only apply when those conditions are met. There is no mechanism for governance to slash everyone unconditionally.
A proposal that attempts to redefine slashing to apply universally would require changing core logic, which governance alone cannot do.
3. Governance Process Safeguards
Even before a proposal reaches execution, governance systems usually include:
Proposal deposits to discourage spam
Quorum requirements that scale with stake distribution
Time delays between vote approval and execution
These delays matter. They give the ecosystem time to react—by exiting positions, mobilizing counter-votes, or coordinating emergency responses if something genuinely dangerous appears.
Governance is slow on purpose. That slowness is a feature, not a flaw.
4. Economic Reality of Governance Attacks
There’s also a less technical but equally important constraint: cost.
To pass a malicious proposal, an attacker would need to control a significant portion of WAL voting power. Acquiring that stake is expensive, and using it to destroy the network would directly devalue the attacker’s own holdings.
This doesn’t make attacks impossible, but it raises the bar high enough that “burn everything” proposals are economically irrational rather than just technically blocked.
The Real Governance Risk Is More Subtle
When I think honestly about governance risk in WAL, I don’t worry about cartoonishly evil proposals like 100% slashing for everyone. Those are easy to detect and easy to stop.
The real risks are quieter:
Gradual increases in penalties that disproportionately affect smaller operators
Parameter changes that subtly centralize participation over time
Governance apathy that allows a small group to dominate voting
These are the kinds of governance failures that don’t look malicious in isolation but compound over time.
And importantly, they are not unique to WAL. They exist in every token-governed system.
How WAL’s Design Mitigates These Subtle Risks
From what I can observe, WAL governance mitigates long-term risk through structure rather than promises.
Bounded parameters prevent runaway outcomes.
Delayed execution allows social coordination.
On-chain transparency makes changes visible and auditable.
Most importantly, governance does not operate in isolation. Node operators, developers, and users all respond to governance outcomes economically. If a parameter change makes participation unattractive, the network feels it quickly.
That feedback loop is not perfect, but it is real.
Governance as a Shared Responsibility
One conclusion I keep returning to is that governance safety is not just a technical problem. It’s also a social one.
No amount of parameter bounding can fully compensate for:
Low voter participation
Concentrated token ownership
Lack of critical review of proposals
WAL governance, like any governance system, depends on active, informed participation. The protocol can prevent extreme damage, but it cannot force good judgment.
Final Reflection
So, could a malicious proposal like “slash everyone 100%” be passed and executed through WAL governance?
Realistically, no. Protocol-level constraints, conditional enforcement, governance safeguards, and economic disincentives all work together to prevent that kind of catastrophic outcome.
But governance risk doesn’t disappear just because the worst-case scenario is unlikely. It shifts into more nuanced territory: parameter drift, centralization pressure, and voter complacency.
Understanding that distinction is what turns governance from a buzzword into a responsibility. And for WAL, that responsibility is shared—not just by developers or large holders, but by anyone who participates in shaping the system’s future.

