
"Hey Bro, I recently heard about Reentrancy Attacks, but don't have any idea about it. What's that Bro?"
Bro, imagine you go to a bank where the teller is extremely slow and has short-term memory loss.
You walk up and say, "I'd like to withdraw $100."
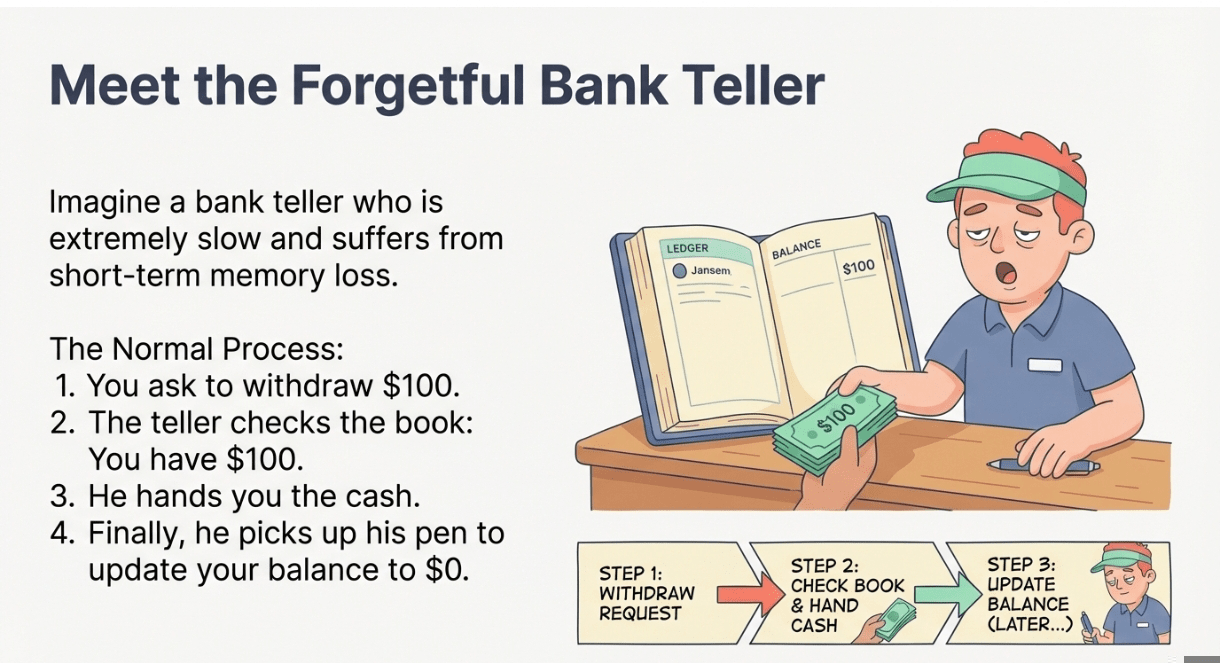
The teller checks his book, sees you have $100, opens the drawer, and hands you the cash.
BUT, strictly before he picks up his pen to update your balance to $0, you interrupt him and shout:
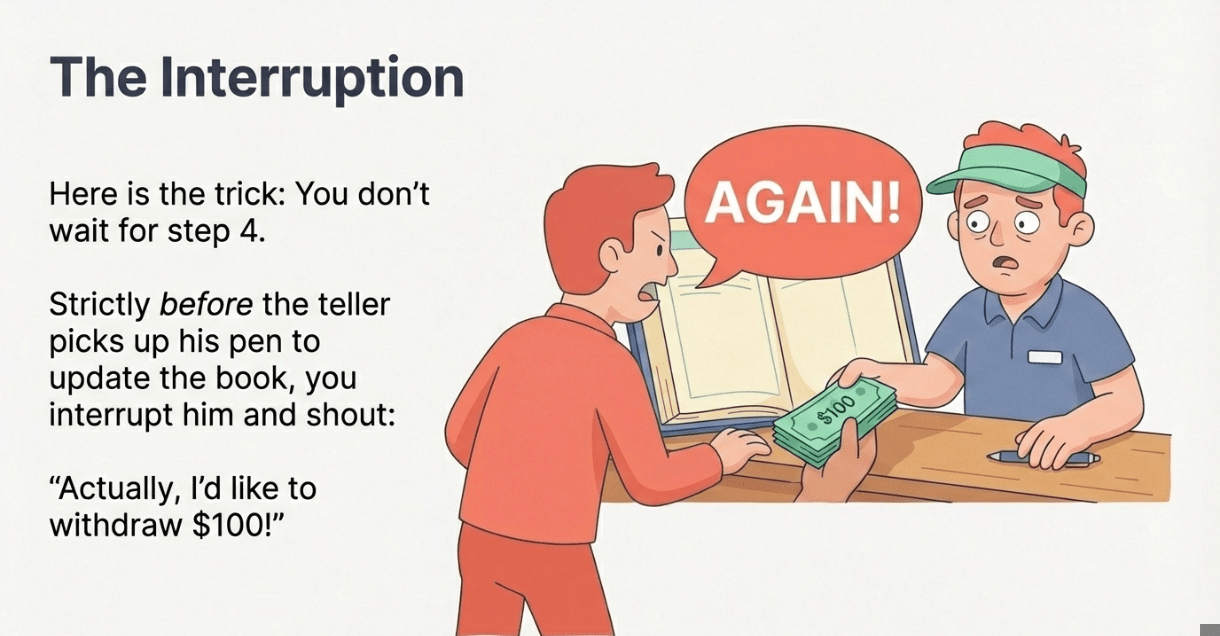
"Actually, I'd like to withdraw $100!"
He looks at the book. Since he hasn't written anything down yet, the book still says you have $100. So he hands you another $100.
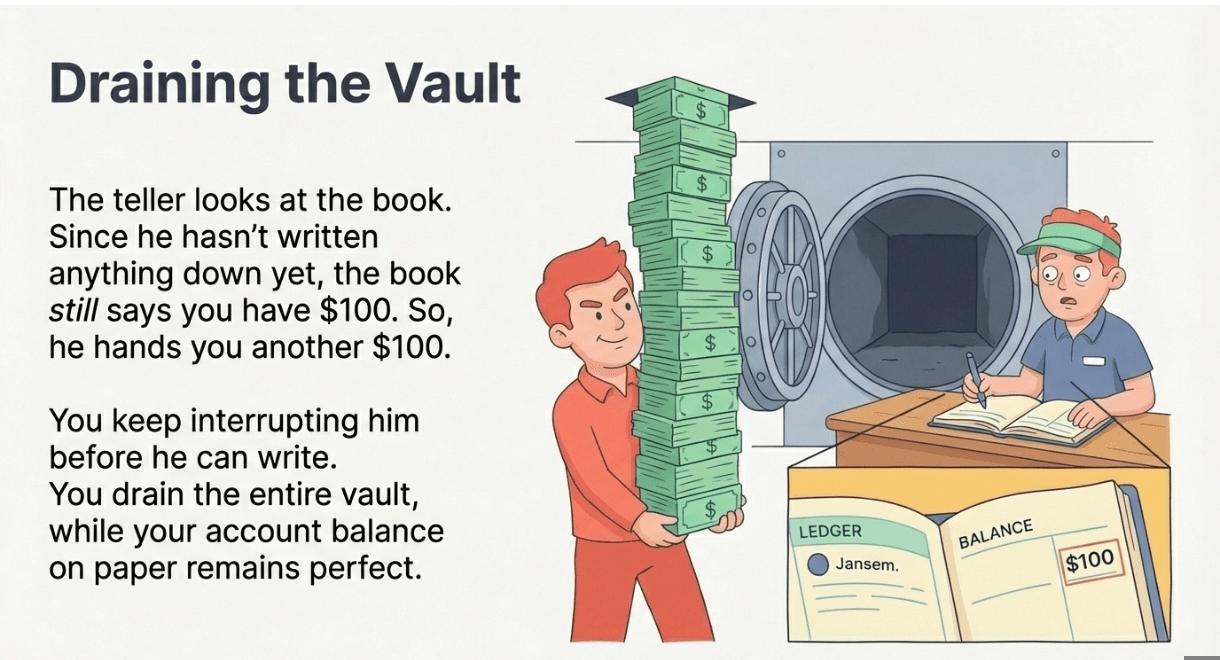
You keep interrupting him before he can write, draining the entire bank vault, while your account balance on paper stays perfect.
That "Infinite Money Glitch" is a Reentrancy Attack.
In a Smart Contract, the code usually does two things when you withdraw:
Send the Money (Hand over the cash).
Update the Ledger (Subtract the amount from your balance).
If the developer writes the code in that exact order (Send -> Update), they are doomed.
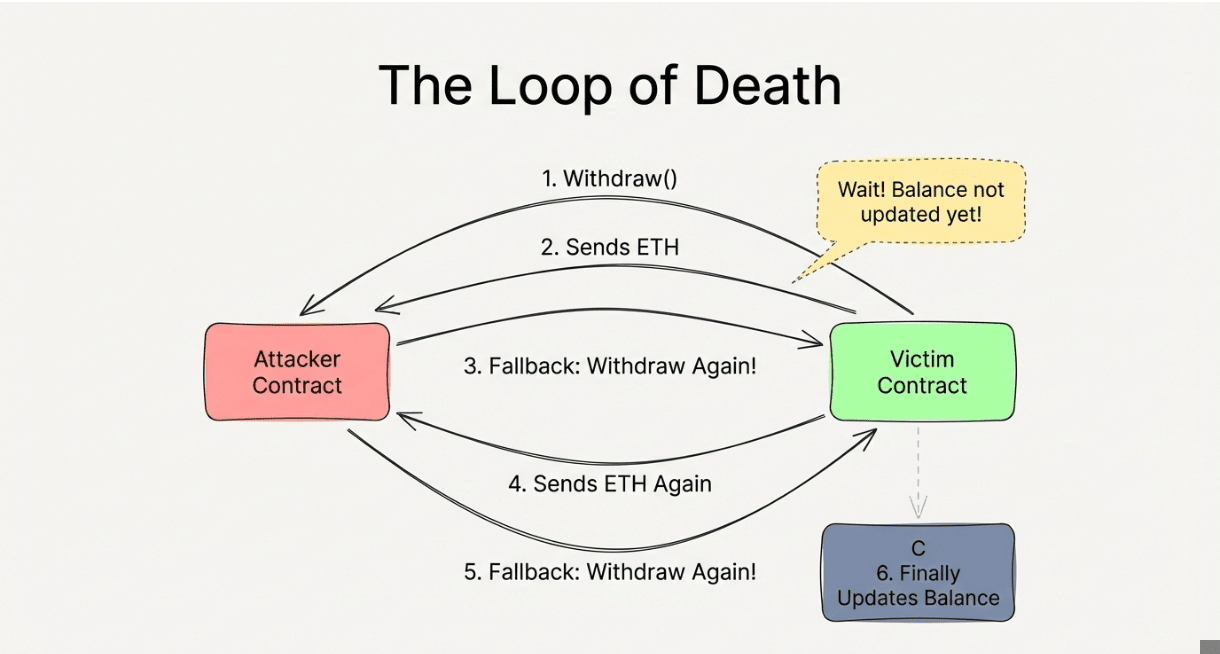
An attacker writes a malicious contract that automatically shouts "Withdraw again!" the millisecond it receives the money. Because the main contract hasn't reached step 2 yet (Update Ledger), it thinks the user still has funds and sends the money again. It loops this process until the contract is empty.
Okay, but how does it actually work?
Here are a couple of details that didn't fit the simple analogy:
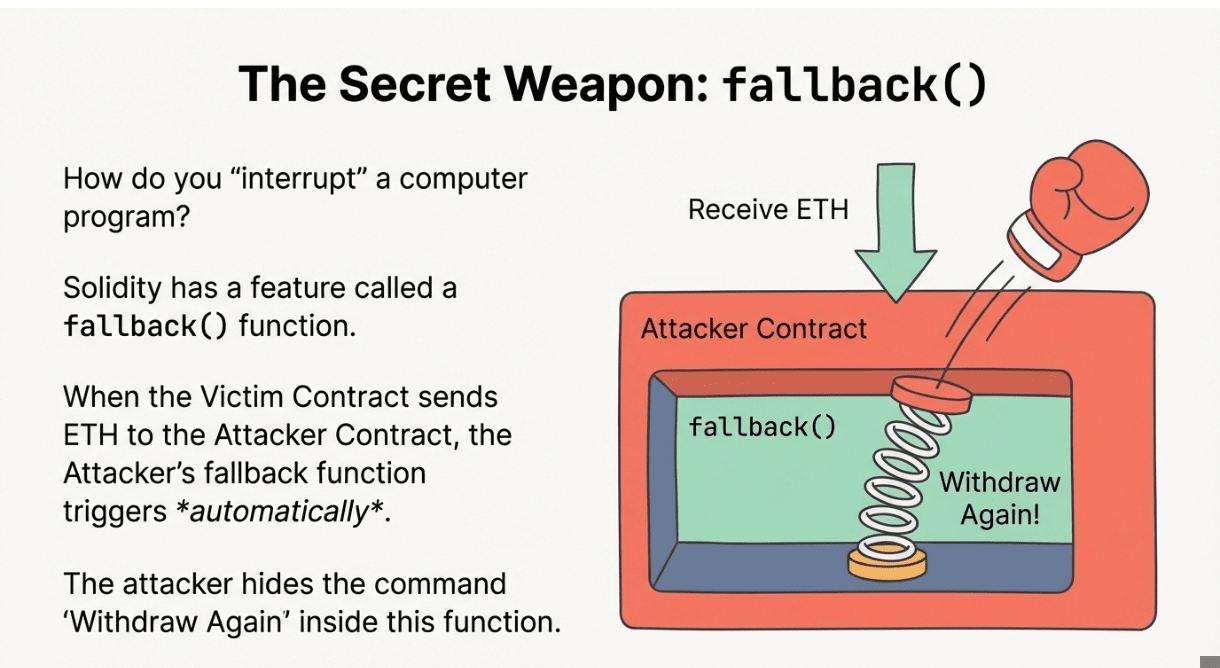
The Fallback Function: The "Interruption" happens because of a special feature in Solidity called a fallback() function. When the Victim Contract sends ETH to the Attacker Contract, the Attacker's fallback() function triggers automatically. The attacker hides the "Withdraw Again" command inside this function.
The Fix (Checks-Effects-Interactions): The way to stop this is simple but easy to forget. You must update the ledger before you send the money. If the teller writes "-$100" in the book before opening the cash drawer, the attack fails. This is called the "Checks-Effects-Interactions" pattern.
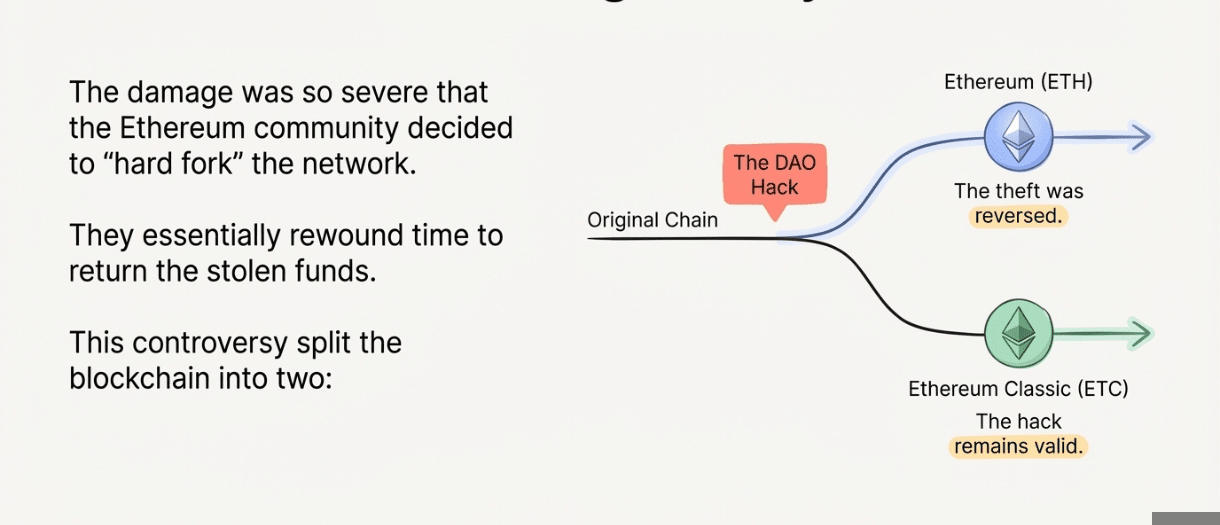
This is the specific hack that killed "The DAO" in 2016 (the first major crypto fund). It was so bad ($60 million stolen) that Ethereum had to "hard fork" (we already discussed about it) to fix it, which is why we have Ethereum (ETH) and Ethereum Classic (ETC) today. It is the grandfather of all smart contract exploits.



