A few years ago I kept running into the same wall while reviewing “privacy” chains for finance: either everything was public (easy to audit, hard to use), or everything was hidden (easy to use, hard to supervise). When I dug into Dusk Foundation, I tried to read it like an operator: where exactly do rules get enforced, and where does privacy actually start?
The friction is that regulated activity needs constraints who can interact, which assets can move, whether limits were respected yet markets also need confidentiality for balances, counterparties, and strategy. If compliance is only off-chain, the ledger can’t validate that the right rules were followed; if everything is transparent, the audit trail becomes a data leak.It’s like processing sealed documents at a checkpoint: the guard should verify the stamp and expiry date without opening the envelope.
The network’s core move is to make “rules” part of transaction validity, while keeping “details” behind proofs and selective disclosure. The 2024 whitepaper positions privacy and compliance as co-requirements, and it leans on two transaction models so applications can choose what must be public versus what can be proven.
At the base layer, finality and accountability are handled with a committee-based Proof-of-Stake design. Succinct Attestation runs proposal → validation → ratification rounds with randomly selected provisioners and committees. The protocol also defines suspension plus soft and hard slashing for faults like missed duties, invalid blocks, or double voting.
For state and transaction flow, the Transfer Contract is the entry point and it supports two models. Moonlight is account-based: balances and nonces live in global state, and the chain checks signatures, replay protection, and fee coverage directly (gas limit × gas price). Phoenix is note-based: value is committed and the opening is encrypted for the recipient’s view key, notes sit in a Merkle tree, spends reference a recent root, nullifiers prevent double-spending, and a zero-knowledge proof asserts ownership, balance integrity, and fee payment conditions without exposing the private amounts.
“Compliant” here isn’t a master key; it’s giving applications primitives to demand eligibility proofs while keeping disclosures minimal. Citadel is described as a self-sovereign identity layer that can prove attributes like age threshold or jurisdiction without revealing exact identity data. Zedger is described as an asset protocol for regulated instruments, including mechanics like capped transfers, redemption, and application-layer voting/dividend flows.Execution support matters because privacy proofs are expensive if verification isn’t first-class. The 2024 whitepaper describes a WASM-focused VM (Piecrust) and host functions for proof verification and signature checks, so every node can reproduce cryptographic results while keeping contract code modular.
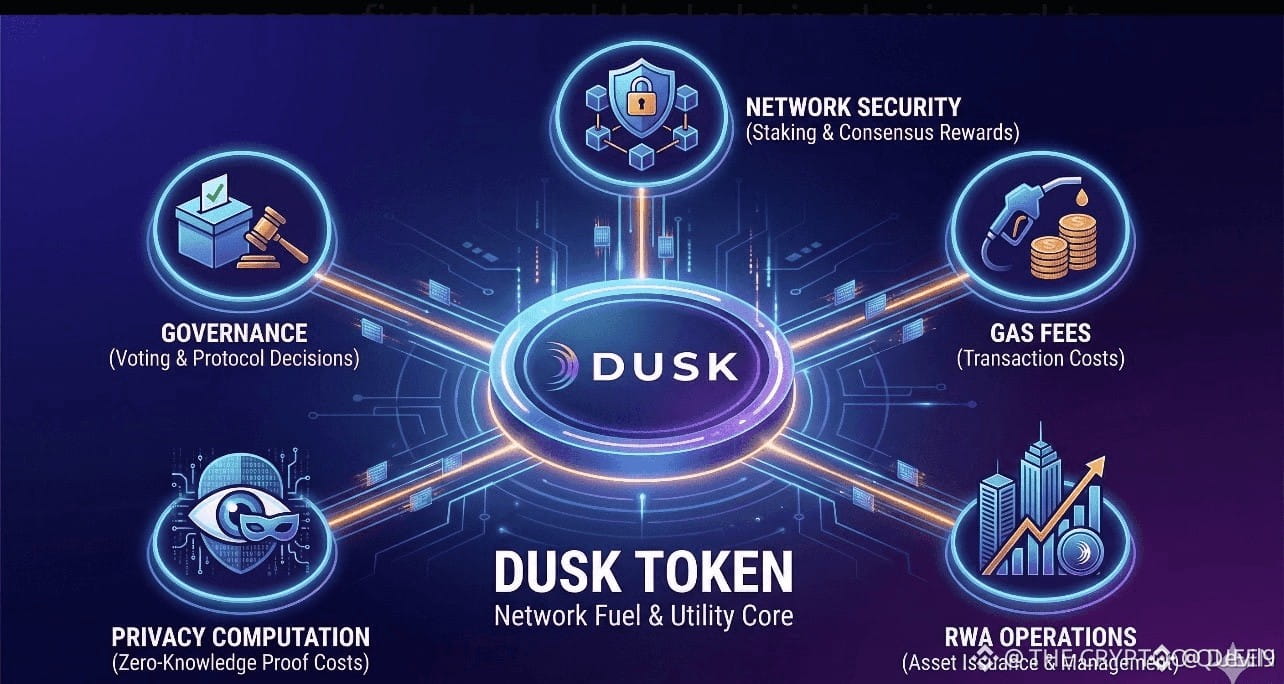
Token utility then lines up with the security model rather than narrative. DUSK is used to stake for consensus participation and rewards, and it pays network fees and gas (quoted in LUX). In the modular stack description, the same token is positioned for governance and settlement on the base layer while remaining the gas asset on execution layers; and protocol changes are tracked through Dusk Improvement Proposals as a structured governance record.
My uncertainty is that cryptography can prove constraints were satisfied, but real-world “compliance” still depends on how consistently applications wire these proofs into policy, and on what external regulators accept over time.
@Dusk #Dusk $DUSK