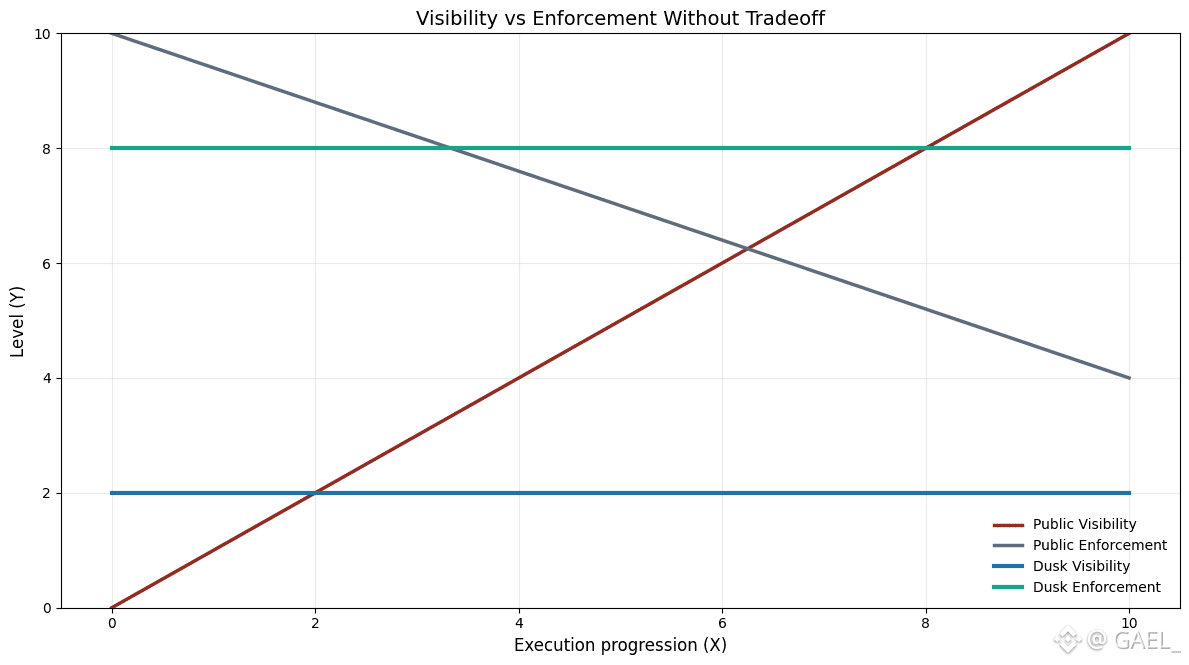
Secrecy execution and regulatory compliance are the two opposing goals that are often framed. Privacy restricts visibility whereas compliance is believed to need transparency. With this tension the much of blockchain design is built around the principles of public execution which needs to be verifiable and compliance moved off-chain or dealt with through other methods. In case of controlled finance this model is weak. It supposes that the cost of enforcement is exposure.
@Dusk Foundation is premised on another belief: confidentiality and compliance do not conflict as long as they are implemented simultaneously on the protocol level.
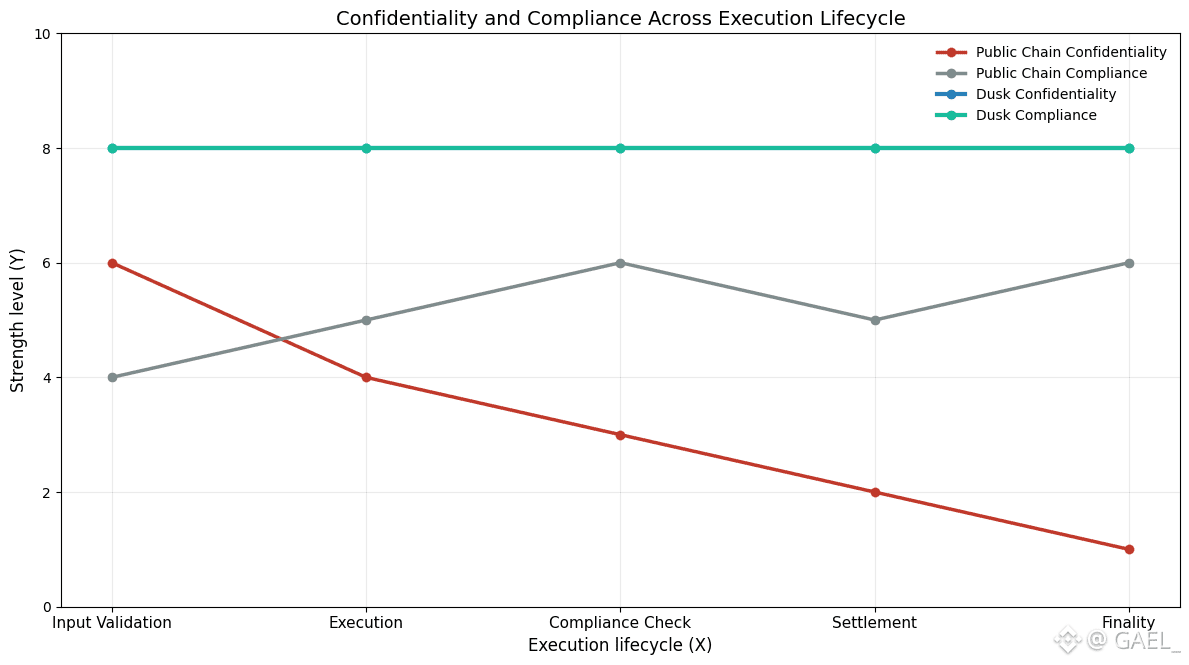
@Dusk allows covert action by isolating what has to be checked and what has to be seen. The transactions and smart contracts run in a secretive setting with the default protection on inputs, internal algorithms, and delicate changes in the state. Validators can still be assured that everything is being run properly but they do not get access to the financial details. This difference is necessary in institutions that are unable to publicize pricing models, allocation rules or the counterparties on a ledger.
Regardless, confidentiality is not the only solution to requirements of regulations. A system that conceals information, but is unable to impose rules on a regular basis is inappropriate in a regulated asset. @Dusk tackles it by applying compliance as a part of transaction validity. Rules of compliance are not optional inspections that should be conducted at the end of a certain execution, but rather requirements prior to a specific execution to be allowed at all.
These implications of design are significant. Permissioned gateways or alternative off-chain registries are used in numerous blockchain projects to enforce compliance; it is thought that compliance should be managed by organizations outside the execution layer. Such strategies bring in fragmentation. On-chain transfer of assets may be technically possible, and off-chain legally prohibited. The outcome is the discrepancy between what is permitted under the protocol and what is willed by regulation.
@Dusk bridges this divide by making sure that compliance limits are imposed even in the process of execution. Eligibility checks, transfer controls, and jurisdictional regulations can be represented as implementation logic of the contract and checked by the protocol. In case a transaction does not obey those constraints, it is just invalid. There is no dependency on external forces to step in post factum.
Most importantly, this enforcement is not obligatory to be disclosed publicly. Checks of compliance can be done on confidential information without exposing the information to the network. This is an opportunity that enables Dusk to reflect the way the compliance works in the traditional financial infrastructure where regulators and auditors are allowed to access the information when needed, but no sensitive information is revealed to all the actors.
Here, selective disclosure is significant. Dusk is pro-controlled visibility, which allows authorized readers to monitor operations via transactions or states at specific circumstances. This will give it the functionality to be audited and legally responsible without compromising with privacy assurances that the institutions rely on. Evidence is relative and not absolute.
Settlement is another aspect that is advantageous to the approach taken by @Dusk . Even where the execution is partially confidential, on most platforms, final settlement is brought to the fore, once again exposing it at the most vulnerable stage in the lifecycle. Dusk considers settlement as an extension of secret execution. A change of ownership and finality takes place under the same confidentiality and compliance assumptions that precede the previous stages. This does not allow the case of compliance being weakened at the point of greatest legal impact.
This architecture makes development easier to the builders. Applications do not have to be rewritten to meet the constraints of public execution or strata level compliance systems. The developers are allowed to model the financial workflows the way they are in controlled conditions, and are confident that the protocol will enforce not only correctness, but compliance as well, without revealing any sensitive code.
The institutional aspect of the benefit is predictability. Risk evaluation, system and legal frameworks, and operational processes can be constructed around a framework in which privacy and enforcement are stable attributes of the protocol, that is not reliant upon the external layers functioning appropriately. This minimizes technical as well as regulatory risk.
After all, @Dusk shows that secrecy does not mean that compliance should be undermined. Making both first-class protocol properties allows an agent to conduct financial business privately by default, by design, and in line with regulatory reality. It is not the optimization of existing blockchain models it is an infrastructure designed to meet the limitations of regulated finance in the first place.