@Dusk There’s a funny thing about operator guides: they look like dry setup notes, but they quietly reveal how a network expects to survive real usage. Dusk Network’s Node Operator documentation reads like it was written for people who understand what “production” actually feels like—when latency isn’t theoretical, disk isn’t infinite, and one sloppy secret can turn into a week of damage control. That’s why the guide keeps coming back to roles, ports, keys, and storage. None of it is glamorous, but it’s the honest work. And it fits Dusk’s bigger goal: a privacy-preserving chain that still holds up in regulated finance—where audit trails and reliability matter just as much as the cryptography.
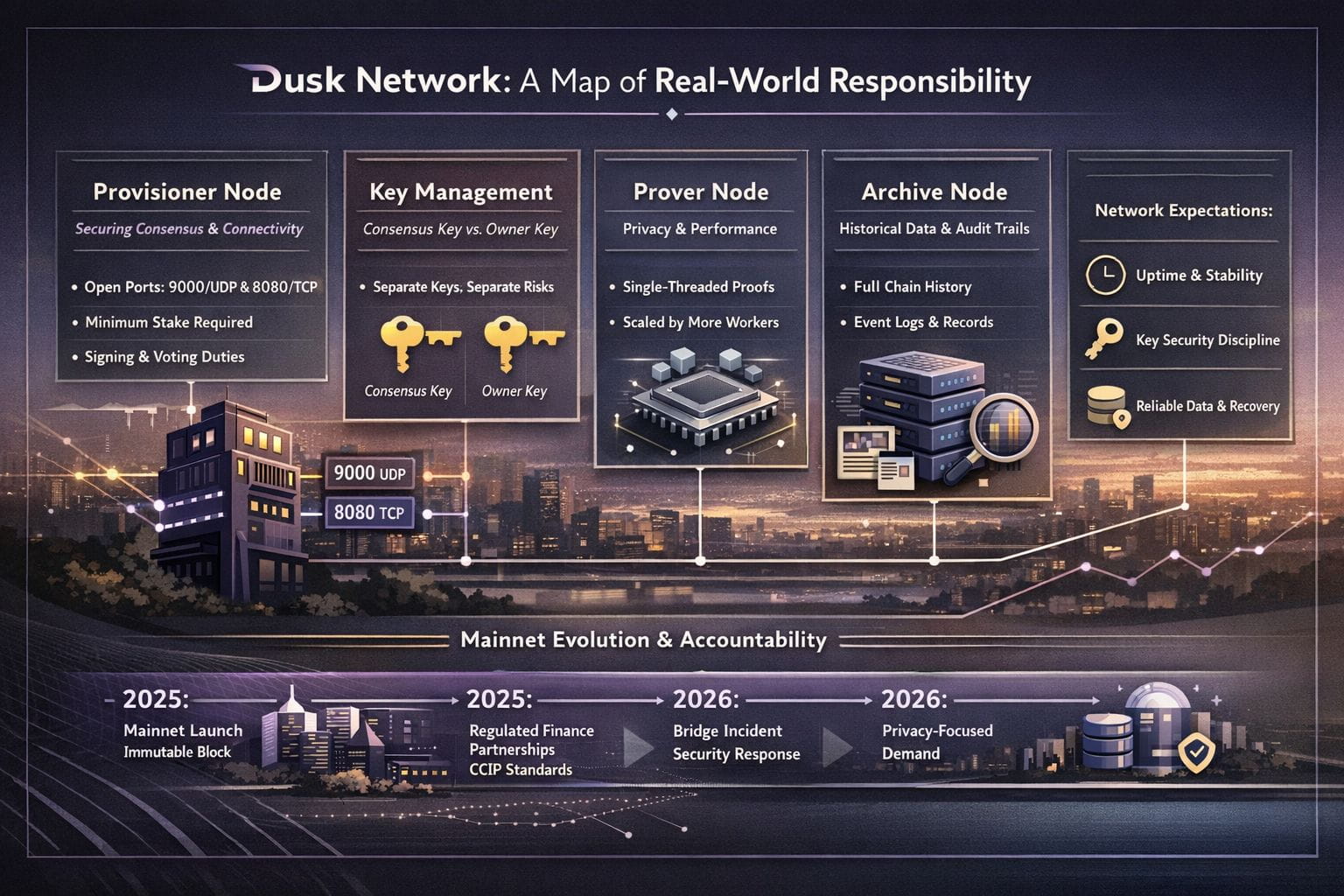
The role the docs put front and center is the provisioner. In normal language, this is the node you run when you want to help the network produce blocks and stay in agreement. The provisioner guide spells out something that sounds small until you’ve been burned by it: Rusk relies on Kadcast over UDP, and you need to open 9000/udp or you’re simply not going to behave like a real peer. It also mentions opening 8080/tcp in certain setups—useful if you’re exposing the node’s HTTP interface or supporting other services that need chain data. This is the sort of detail that separates “I installed a node” from “I’m actually participating.” Connectivity isn’t a nice-to-have in consensus; it’s the difference between being present and being invisible.
What’s also very “operator-brained” is how Dusk talks about stakes and accountability. Provisioners are described as the backbone of security and validation, and the docs state a minimum stake requirement to participate in consensus. Whether someone agrees with that threshold or not, it reinforces a point the guide never has to say out loud: running this role is not casual. You are signing, voting, staying online, upgrading on time, and dealing with the fact that misconfiguration can have consequences beyond your own machine.
Key handling is where the responsibility gets sharper. Dusk’s wallet and staking documentation draws a clear line between the consensus key (used to participate in consensus) and the owner key (the one entitled to unstake or withdraw). It even notes that, by default, they can be the same unless you explicitly set an owner key, which is both convenient and slightly unsettling if you’ve seen how often “defaults” become permanent habits. The most mature infrastructure cultures are the ones that assume mistakes will happen and design around blast radius. Separate keys, separate passwords, and minimal permissions for always-on processes isn’t paranoia; it’s basic respect for how messy reality gets.
Then there’s the prover, which quietly reframes privacy as a workload rather than a buzzword. Dusk’s prover guide doesn’t romanticize it. It explains that proof generation is single-threaded, so single-core performance matters, and scaling comes from adding workers rather than hoping one machine magically becomes faster. That kind of specificity is refreshing because it’s the exact opposite of hand-waving. If privacy is part of the network’s promise, then someone has to do the compute reliably, and the docs make it clear Dusk wants operators to think about capacity, not just installation.
Archive nodes add the long memory. The archive node documentation says they provide additional historical data—like events emitted by contracts—that a provisioner node does not store. This matters more than it sounds. In finance-adjacent systems, the question “what happened and when?” is not philosophical. It’s an operational need for applications, auditors, and anyone debugging a dispute. Dusk also frames archive nodes as supportive infrastructure that is not strictly required for consensus participation. In other words, they’re a civic contribution to the network’s clarity and accountability, even when they aren’t the path to rewards.
This all lands differently right now because Dusk has been moving from “documented idea” to “live system people will stress.” In December 2024, the mainnet rollout post laid out a timeline that targeted the first immutable block on January 7, 2025. Not long after, Dusk started framing itself more directly as regulated-market infrastructure—including the November 2025 news that Dusk and NPEX were adopting Chainlink interoperability and data standards like CCIP. Then in January 2026, Dusk published a bridge incident notice about unusual activity linked to a team-managed wallet used for bridge operations, followed by a precautionary pause and the note that—based on what they knew—no user funds were impacted. Add the early-2026 spotlight on privacy-focused assets, and the pattern is familiar: attention goes up, traffic goes up, and expectations go up right along with it.
If you want the title to mean something—“real-world responsibility”—the operator guide is where that meaning shows up. Dusk’s documentation is essentially a checklist of what the network will demand from adults in the room: stable networking, disciplined key separation, honest compute planning for proving, and archival infrastructure that makes the chain legible over time. It doesn’t guarantee success. But it does suggest a network that expects to be judged the way serious systems are judged: by uptime, recoverability, and whether the boring parts were treated as first-class citizens.
