I remember very clearly the moment I saw Fogo proactively hit the brakes with the pause module. The feeling was not panic but a kind of chill, because at least they admitted the system was having a problem.
In this market, incidents do not surprise me anymore. What I notice is how a team sets limits on its own power. With Fogo, the discussion sits in four pieces: a pause module to stop spread, a timelock to lock time for sensitive changes, a multisig to distribute the button, and community notice to reduce noise. Saying it is complete is easy, saying it is proven is harder, because veteran users look at operational traces, not at reassurance.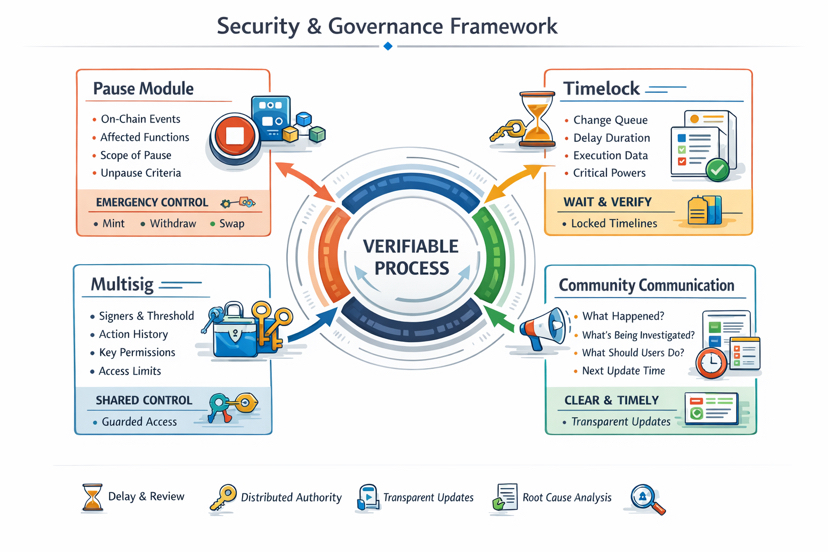
With the pause module, I always want to see two layers of data. The first layer is on chain data: which contract address actually receives the pause command, which event is emitted, which block time marks the moment the system changes state, and what pattern of reverts appears after that. The second layer is product data: whether the pause locks the risky part or locks the whole system, for example only stopping mint, stopping withdraw, stopping swap, or stopping every key entrypoint. If Fogo only says it has paused for safety but does not show the scope and the unpause criteria, users are forced to trust a feeling. If Fogo provides a list of affected functions, an estimate of impact, and the next update time, pause is no longer a symbol of control, it becomes an emergency mechanism with clear boundary.
Timelock is the test of discipline, and here I look at specifics. A real timelock is not a line in documentation, it is a contract with a queue and a waiting time. You can check when a sensitive change is queued, how long the execute delay is, what call data is waiting, and whether execution matches what was queued when the time comes. It is ironic that many teams say they have timelock but leave dangerous power outside timelock, so the community only watches after the movie is already over. With Fogo, I want clarity on whether timelock applies to powers like proxy upgrade, risk parameter change, fee change, limit change, oracle config change, or only applies to low impact action. And whether the waiting time is enough for outsiders to read, verify, question, or just enough to legalize a decision already made.
Multisig sounds technical, but it is really about human structure. At the data level, multisig is not vague: the multisig wallet address, the threshold m of n, the history of signed transaction, and which contract the wallet can call. At the product level, what matters is what multisig controls, not what multisig is. If multisig can pause, upgrade, change parameter, and reach treasury, then it is a center of power, just a center with many key. I worry less when Fogo multisig is bound by timelock, and every action leaves a public trace users can match, instead of having to trust explanation after that.
Community notice is the software of trust, and I judge it by cadence and structure, not by feeling. A good notice answers four question in order: what is confirmed, what is being investigated, what user needs to do right now, and when the next update is. If it only says fund is safe without scope, without timeline, without matching product state change, that is empty word. If Fogo has a status page or a single thread organized by timeline with block time marker for cross check, community noise drops a lot. This sounds simple, but few project do it clean under stress.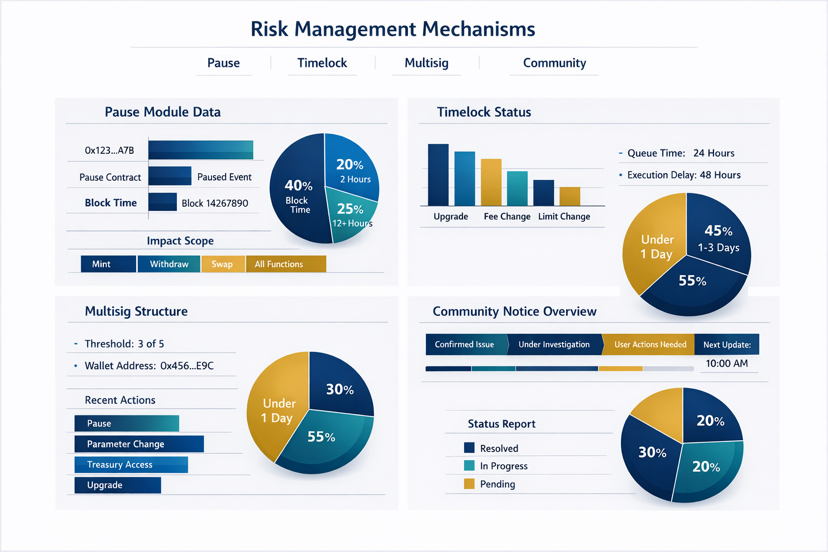
Looking deeper, the four pieces only matter when they connect into a closed process that can be verified. Pause buys time, timelock forces change through daylight, multisig avoids one sided decision, and communication reduces noise. If one link becomes a formality, the whole chain bends, and veteran user will smell it immediately. What I want to see at Fogo is a clear authority map: who can propose, who can sign, who can execute, and what time constraint or oversight binds each action, so no one can both play and referee.
I also watch whether they write a postmortem that can be cross checked. A good postmortem states root cause, impact scope, response timeline, wrong assumption, and concrete change in contract configuration or operational process. It does not need fancy word, it only needs to be correct and consistent with on chain data: event, permission, parameter, and change history. If Fogo does this seriously, the community does not just hear a story, it can verify the story.
What makes me keep tracking Fogo is not a promise of safety, but how they turn safety into something measurable: pause state has scope, timelock has queue and waiting time, multisig has bound authority, and notice has a timeline that can be matched. So when another crisis comes at the hottest moment of the market, will Fogo keep that measurable discipline, or loosen it to chase crowd tempo.